The Dataset
Snopes was able to identify apparent clients of Maxpay using a combination of tools.
Our primary dataset originated from analysis performed by the business intelligence and website analytics company SimilarWeb, which provided Snopes with a list of referral data to the website maxpay.com for the period of time spanning December 2020 to November 2021. The SimilarWeb data reveal 408,573 referrals from 144 domains. The majority of referral traffic comes from URLs whose websites do not ever mention or publicly link to Maxpay.
These data refer to times in which a user arrives at or connects to maxpay.com from an external website. A common way to think of a referral is a user who has clicked on a link on one website to arrive at another, but such data could also reveal times in which components of one website connect to maxpay.com to perform some function, service, or monitoring.
Verifying a Connection to Maxpay
To test the hypothesis that this subset of referral traffic could come from processing payment information on external websites, Snopes analyzed each of these domains — either from their live versions or, in cases in which the websites had been removed, from archived data captured by either Archive.org's Wayback Machine or urlscan.io. The latter is a website that logs, categorizes, and archives myriad aspects of a URL, its function, and its communication with other websites at a given point in time.
As an example, get.booklounge.net is the second most significant source of referral traffic to maxpay.com. An attempt to load this website, at the time of this reporting, displays only a blank screen with the text "ok." This is, at least in part, because content only appears at this web address if its url contains a specific page and contains tracking tags. These tags (the text that appears after a question mark in a URL) serve a few purposes. They tie the visit to a specific affiliate marketer for the purpose of compensation, and they also dictate what content appears on the page itself.
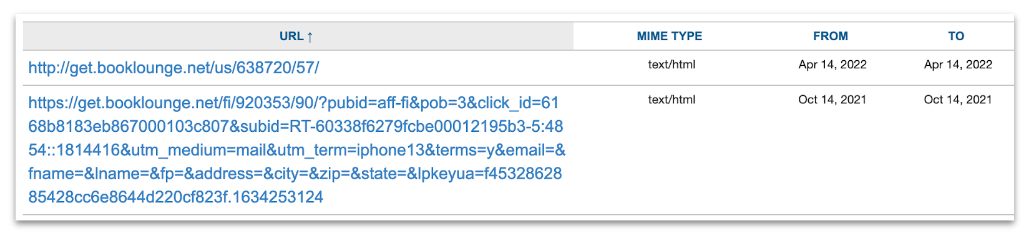
Finding archived copies of the full URLs is the best way to view the versions of the site that their potential customers would see. One place to hunt for these snapshots is Archive.org's Wayback Machine. Entering the web address get.booklounge.net* (with a * appended to the end) creates search for all archives of that website that begin with that URL. In the case of booklounge.net and many others, such a search reveals functional URLs:
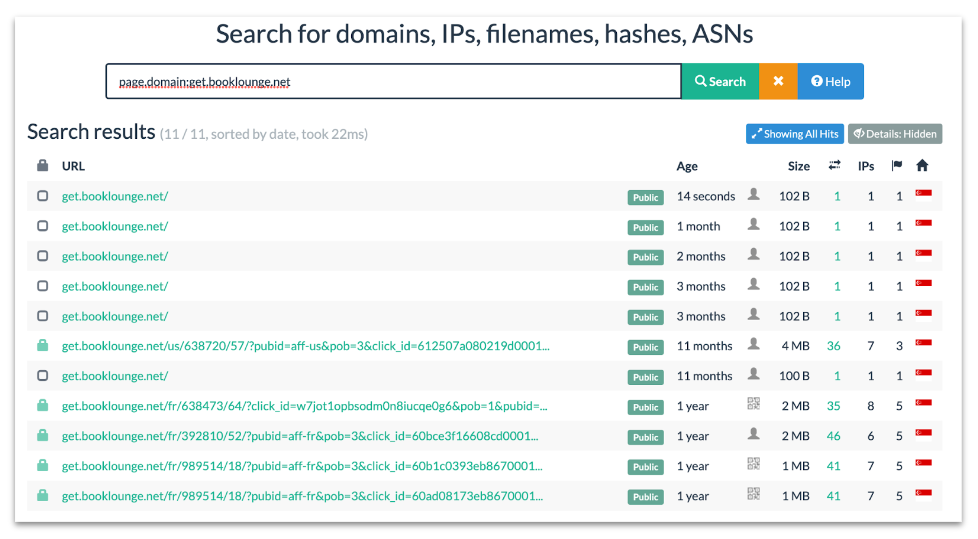
Another method uses the tool urlscan.io. Similar to Archive.org, this site also archives information from past versions of websites, but it does so with a focus on logging a website's behavior and identifiers helpful in linking related enterprises. At this website, a search for get.booklounge.net reveals several full Book Lounge URLs as well:
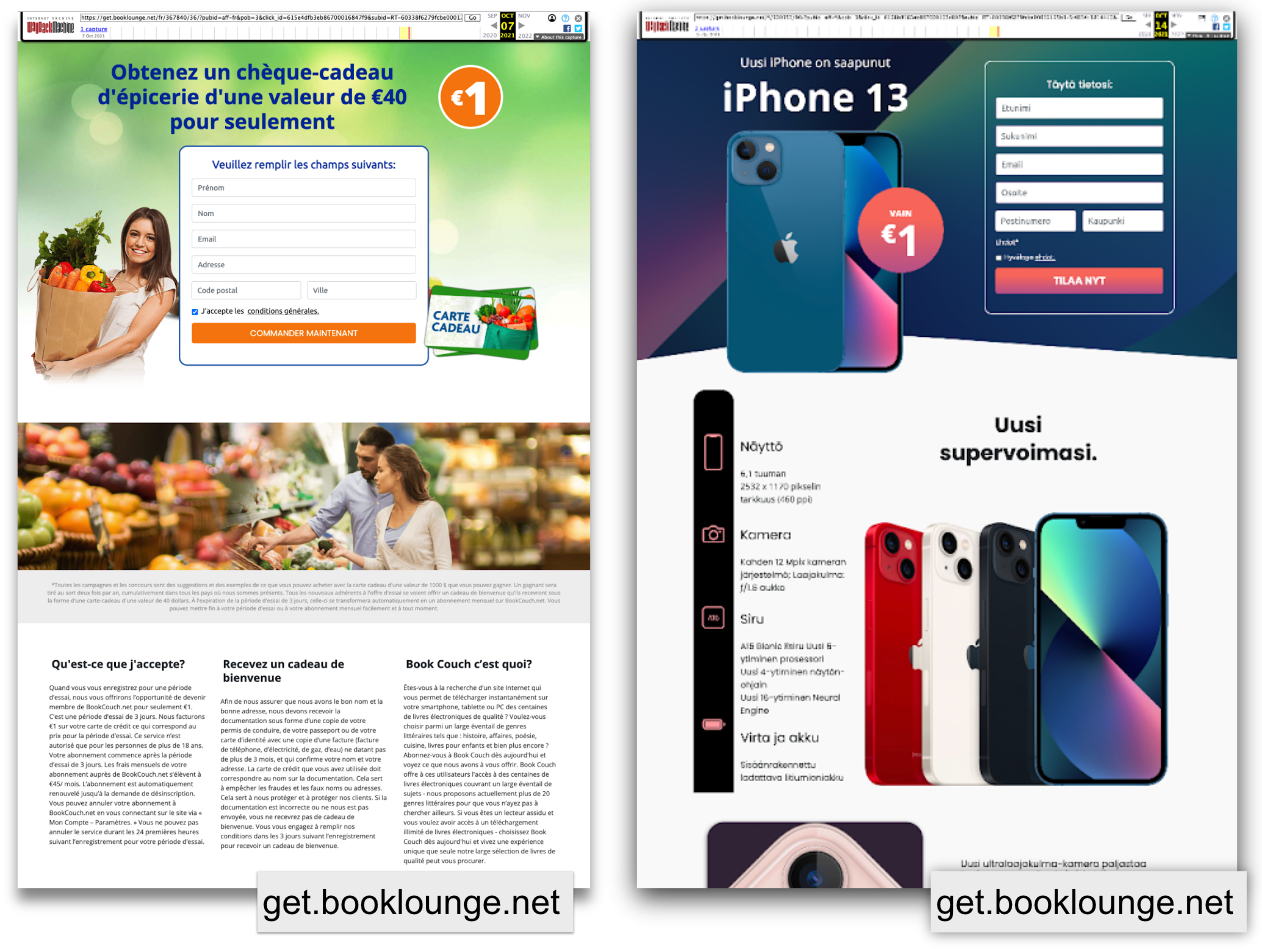
That website, booklounge.net, which is discussed in detail in part two of this series, purports to be an ebook subscription service. It is, however, a front for predatory sweepstakes contests purporting to enter registrants into a chance to win a variety of prizes after they provide a credit card number. These full addresses reveal landing pages where visitors enter such raffles without realizing they are also signing up for an expensive recurring monthly charge:
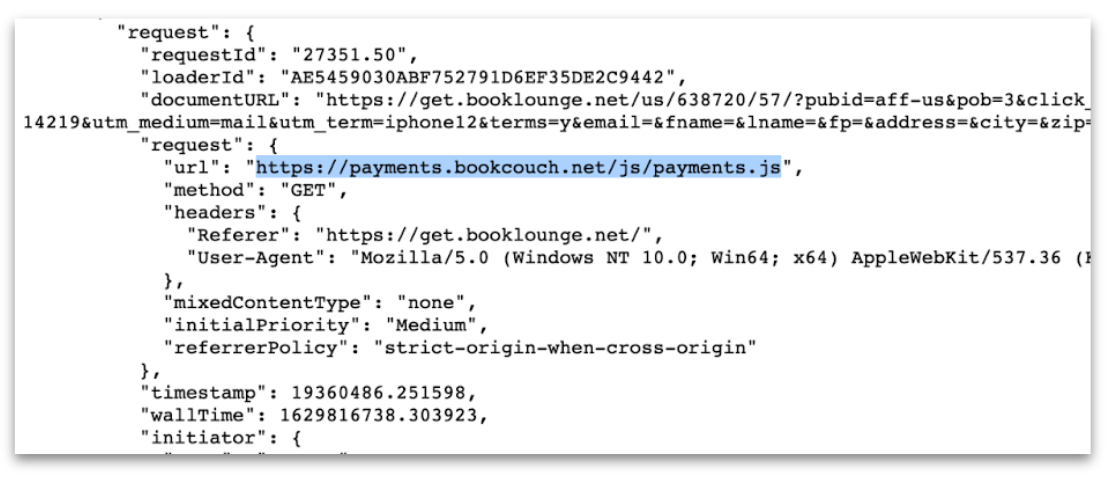
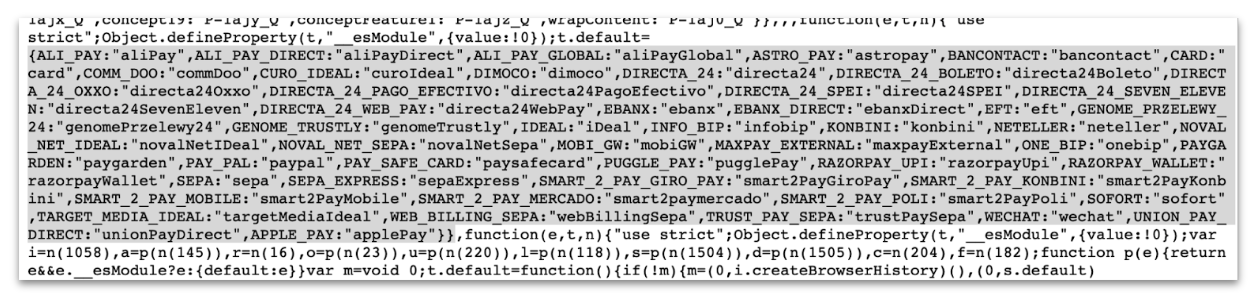
These .js files can be viewed in source form on a regular web browser. This code, Snopes found, is what betrays booklounge.net's connection to maxpay.com and provides what we interpret to be the cause of the referral to maxpay.com logged in the SimilarWeb data:
Booklounge URLs also record evidence of this same link to Maxpay when analyzed by urlscan.io:
Both of these landing pages were archived within the window of time covered by the SimilarWeb referral data. These combinations of factors — referral data from SimilarWeb and source code information independently collected by Snopes — led us to conclude that many of the URLs in our dataset are or were from websites apparently utilizing a Maxpay service in some way. The complete table with these added data can be found here:
[Maxpay Apparent Client Spreadsheets]
Snopes discovered 14 broad classifications of apparent clients. A brief discussion of each client type, as well as the verification process we used in each case, is described below. Here is their distribution:
| Classification | Referrals | Percent |
| Dating* | 97846 | 23.9% |
| E-books* | 55491 | 13.6% |
| Regular Builder Portal* | 73345 | 18.0% |
| Merchant Service | 61812 | 15.1% |
| Account Trading | 55853 | 13.7% |
| Fitness* | 22008 | 5.4% |
| Unknown | 15059 | 3.7% |
| Software/Service | 13238 | 3.2% |
| Budgeting* | 6555 | 1.6% |
| Referral/Media Link | 2521 | 0.6% |
| Casino | 2267 | 0.6% |
| Banking Institution | 1476 | 0.4% |
| Games | 896 | 0.2% |
| Internal Link | 206 | 0.1% |
Subscription trap scams are found in several of these categories and, as a unit, account for 61.6% of referral traffic to Maxpay.com.
Together Networks/Other Dating Websites (24%):
Nearly 24% of Maxpay's traffic comes from online dating websites associated with these URLs:
| URL | Referrals | Percent |
| m.onenightfriend.com | 220 | 0.1% |
| m.flirt.com | 620 | 0.2% |
| gift.steadydate.net | 879 | 0.2% |
| campaign.steadydate.net | 1,104 | 0.3% |
| m.uniformdating.com | 3,656 | 0.9% |
| m.tendermeets.com | 26,681 | 6.5% |
| m.benaughty.com | 64,686 | 15.8% |
One Night Friend, Flirt, Uniform Dating, Tender Meets and BeNaughty are all associated with Max Polyakov or Together Networks. The most prevalent dating site was the flagship Be Naughty. Within the period of time covered by our SimilarWeb data, BeNaughty and other related websites ran identical .js files including the phrase chunk.dating that made reference to both Maxpay and Genome, a company connected to Maxpay, in a section of code related to payments:
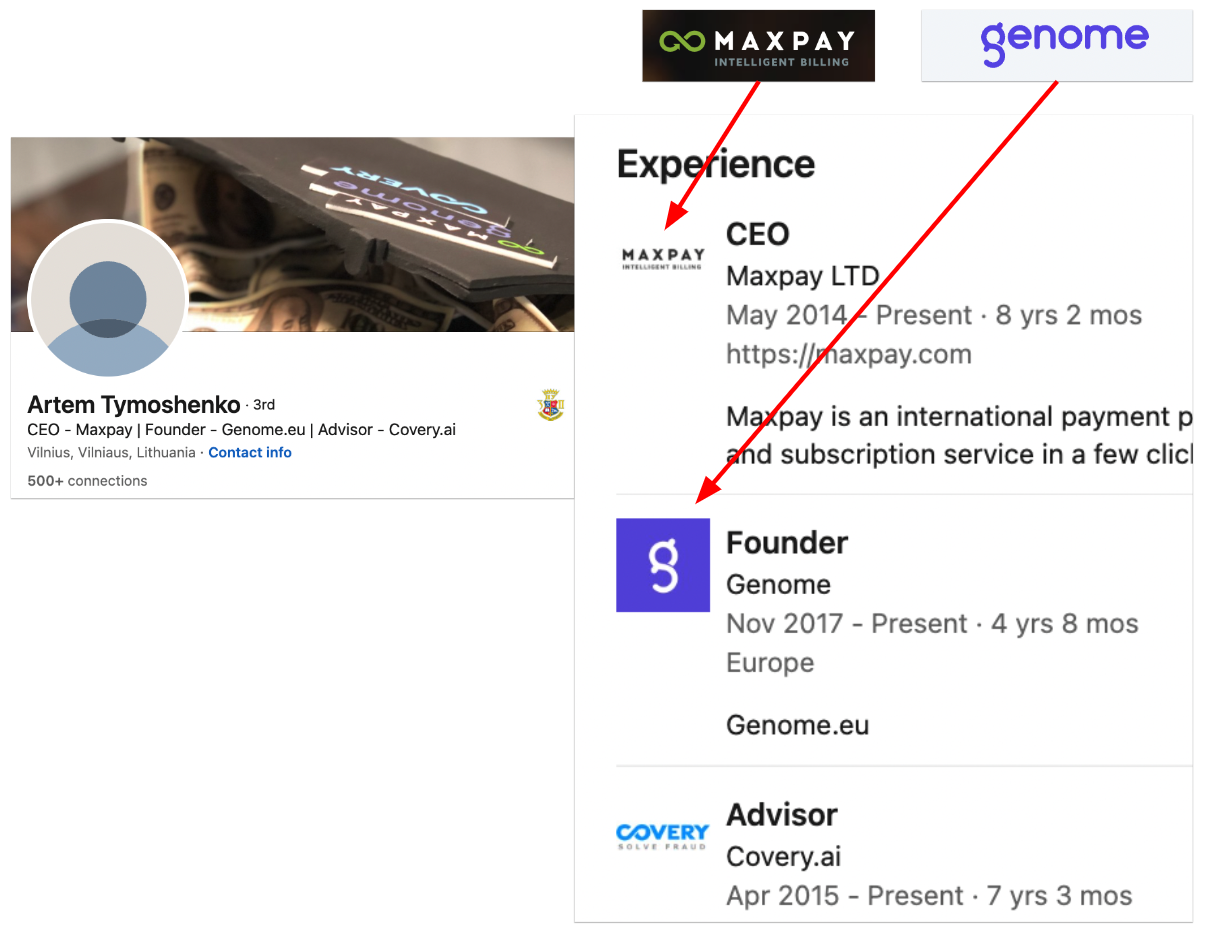
The CEO of Maxpay founded Genome, according to his Linkedin profile:
Fake Merchants Used For Sweepstakes (21%)
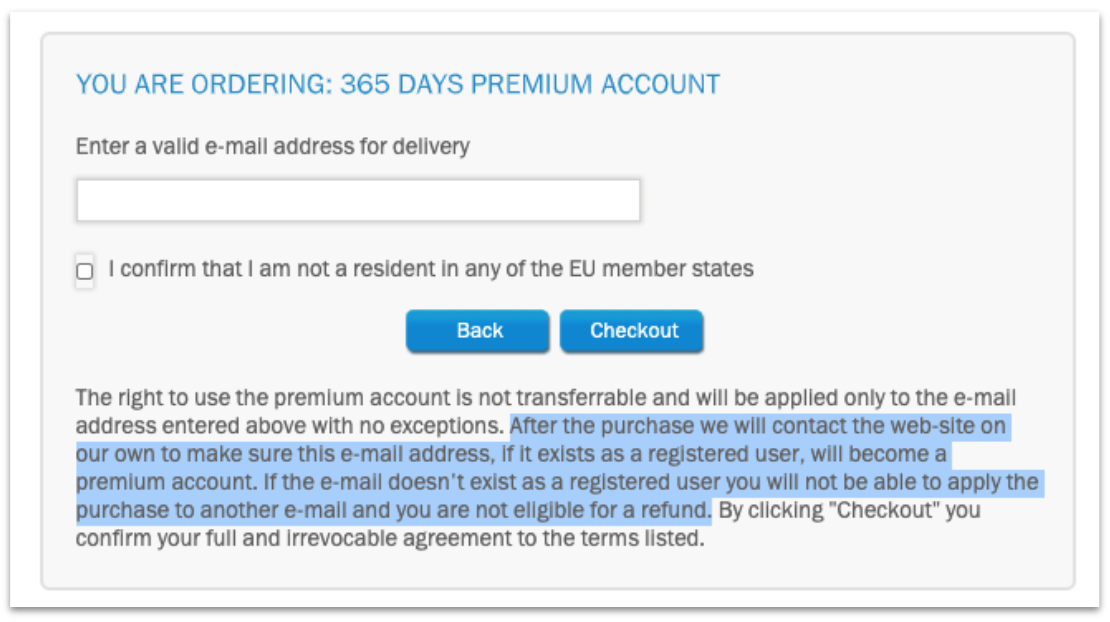
Over 84,000 referrals to maxpay.com come from online merchants that operate in a manner similar to Piggy Budget and Book Lounge, which were described in detail in part two of this series. These subscription-based products, which fall into the categories of e-book libraries, budgeting services, and fitness programs, are in actuality used as companies that "sponsor" sweepstake giveaways requiring a credit card to sign up for that serve to sign individuals up for monthly recurring charges:
| URL | Referrals | Percent | Category |
| obtenir.brainybudgets.fr | 137 | 0.0% | Budgeting |
| welcome.myonlineeconomy.com | 601 | 0.1% | Budgeting |
| welcome.expensefriend.com | 1,785 | 0.4% | Budgeting |
| gift.piggybudget.net | 1,792 | 0.4% | Budgeting |
| letstry.piggybudget.net | 2,240 | 0.5% | Budgeting |
| obtenir.mesebooks.net | 119 | 0.0% | EBooks |
| get.ebookwormers.com | 171 | 0.0% | Ebooks |
| offre.mesebooks.net | 336 | 0.1% | Ebooks |
| offer.ebookcase.net | 535 | 0.1% | Ebooks |
| campaign.ebookwormers.com | 591 | 0.1% | Ebooks |
| c.myebooky.com | 1,238 | 0.3% | Ebooks |
| campaign.ebookcase.net | 3,769 | 0.9% | Ebooks |
| get.booklounge.net | 48,733 | 11.9% | Ebooks |
| gateway.active-healthy.com | 136 | 0.0% | Fitness |
| gateway.workout-master.com | 139 | 0.0% | Fitness |
| gateway.getmeshaped.com | 140 | 0.0% | Fitness |
| gateway.strictlystronger.com | 207 | 0.1% | Fitness |
| gateway.code4fitness.com | 517 | 0.1% | Fitness |
| gateway.sportyflows.com | 1,377 | 0.3% | Fitness |
| gateway.turntosport.com | 1,573 | 0.4% | Fitness |
| gateway.strengthfirst.club | 1,594 | 0.4% | Fitness |
| gateway.cleverbodies.com | 1,633 | 0.4% | Fitness |
| gateway.traintotal.com | 1,755 | 0.4% | Fitness |
| gateway.healthy-avenue.com | 2,118 | 0.5% | Fitness |
| gateway.thebodygoal.com | 2,177 | 0.5% | Fitness |
| gateway.runwaytofit.com | 3,212 | 0.8% | Fitness |
| gateway.endorfinemachine.com | 5,431 | 1.3% | Fitness |
The list below provides evidence of the above URLs being in sweepstakes and other subscription trap schemes within the window of time covered by the Similar Web dataset. Evidence used by Snopes includes scans from urlscan.io, archived pages identified in Archive.org's Wayback Machine, or publicly reported complaints asserting bait-and-switch charges associated with the urls:
- brianybudgets.fr
- myonlineeconomy.com
- expensefriend.com
- piggybudget.net
- mesebooks.net
- ebookcase.net
- myebooky.com
- booklounge.net
- active-healthy.com
- workout-master.com (no record)
- getmeshaped.com
- strictlystronger.com
- code4fitness.com
- sportyflows.com
- turntosport.com
- strengthfirst.club
- cleverbodies.com
- traintotal.com
- healthy-avenue.com (no record)
- thebodygoal.com
- runwaytofit.com
- endorfinemachine.com
Regular Builders, Monitor Builders, and Drive Builders (18%)
An additional 18% of referral traffic to maxpay.com comes from what Snopes classifies as "regular builders" or "drive builders." Similar to the sweep and stream merchants, the urls are associated with payment portals that engage in two forms of subscription trap scams.
Companies and/or products bearing the name Regular Builder, Monitor Builder, or Drive Builder — which claim to provide the software for individuals to monetize their own files or streaming content — are common to each of these payment portals.
These portals are associated with a file-sharing or streaming scheme in which access to a PDF document, e-book, or other file for download is alleged via a trial to file sharing service. In the case of the latter, the portals appear to be associated with offers to stream live sporting events.
A credit card is required for the download or stream to start. After providing this number, a user has signed up for a recurring charge — purported to a file sharing platform or streaming platform. In at least some cases, the credit card entry is predicated on the notion that it is needed to confirm geographic location, and will not actually be charged.
Myriad short-lived URLs have been used for the above purposes but they broadly share several characteristics including use of the ".xyz" top-level domain, the use of a series of letters and dashes that involve portions of the word monitor, regular, drive, and/or builder, and the use of servers housed in Russia.
These varied urls are spread out over only four Russia-based IP addresses, and (in addition to being a source of referral traffic to Maxpay) are connected to Maxpay via their use of Covery. Those domains and their evidence of their use in these scams is detailed below:
| Domain | % | # | IP | Reference |
| drivebook.info | 0.0% | 151 | Unknown | Unknown |
| streaming-monitor.info | 0.0% | 155 | 77.73.69.159 | https://archive.ph/uflgy |
| choicemonitor.top | 0.1% | 210 | 77.73.69.159 | https://archive.ph/fzuZH |
| bulmon.xyz | 0.1% | 214 | 94.242.50.119 | https://archive.ph/6j1G5 |
| bucompact.top | 0.1% | 218 | 77.73.68.49 | https://archive.ph/0vguU |
| bu-ilderegular.buzz | 0.1% | 223 | 77.73.68.49 | https://archive.ph/FKKBz |
| webmoniktor.xyz | 0.1% | 246 | 77.73.69.159 | https://archive.ph/eUvUN |
| mondre.top | 0.1% | 250 | Unknown | |
| mo-ni-tor-bu-ilder.buzz | 0.1% | 288 | Unknown | |
| drumon.xyz | 0.1% | 356 | Unknown | |
| re-dri-ve-buil-der.xyz | 0.1% | 356 | Unknown | |
| dumerobui.xyz | 0.1% | 360 | 94.242.50.119 | https://archive.ph/RkJ3J |
| drivebuilder.xyz | 0.1% | 397 | Unknown | https://archive.ph/SW5J2 |
| regubuil-der.buzz | 0.1% | 427 | Unknown | |
| drivebu-il-der.buzz | 0.1% | 448 | Unknown | |
| drive-bu-il-der.xyz | 0.1% | 471 | 77.73.69.159 | https://archive.ph/mAOVr |
| demonit.xyz | 0.1% | 540 | 77.73.69.159 | |
| minomobu.xyz | 0.1% | 609 | 77.73.69.159 | https://archive.ph/jHhZy |
| mondrive.xyz | 0.2% | 666 | 77.73.67.23 | https://archive.ph/5gg6z |
| bu-ilderegular.xyz | 0.2% | 759 | 94.242.50.119 | https://archive.ph/KBr6D |
| debuil.xyz | 0.2% | 795 | 94.242.50.119 | https://archive.ph/GoG2U |
| buildri.xyz | 0.2% | 801 | 77.73.67.23 | https://archive.ph/EKzTv |
| registeregular.xyz | 0.2% | 908 | 46.227.68.5 | https://archive.ph/lOqqi |
| morebuild.xyz | 0.2% | 921 | Unknown | |
| gumodri.xyz | 0.2% | 967 | 94.242.50.119 | https://archive.ph/CrtFc |
| webregular.xyz | 0.2% | 990 | 94.242.50.119 | https://archive.ph/NAUoP |
| monitordrive.xyz | 0.2% | 1018 | Unknown | https://archive.ph/5sH4k |
| repromonet.xyz | 0.3% | 1053 | 77.73.67.23 | https://archive.ph/5TUWj |
| ebookdrive.online | 0.3% | 1112 | Unknown | https://archive.ph/hnsVI |
| mo-nibuilder.xyz | 0.3% | 1199 | Unknown | https://archive.ph/aY03V |
| monedri.xyz | 0.4% | 1680 | 77.73.69.159 | https://archive.ph/FUkwp |
| builmonire.xyz | 0.4% | 1726 | 94.242.50.119 | https://archive.ph/36Yrq |
| monitorebook.info | 0.4% | 1771 | 77.73.69.159 | https://archive.ph/J4a3z |
| monbuil.xyz | 0.5% | 1884 | 77.73.69.159 | https://archive.ph/7vU4L |
| regudri.xyz | 0.7% | 2831 | 94.242.50.119 | https://archive.ph/9iv1N |
| re-bu-il-der.xyz | 0.7% | 2878 | 77.73.69.159 | https://archive.ph/zlhP2 |
| streaming-builder.com | 0.7% | 3017 | 94.242.50.119 | https://archive.ph/eCxpN |
| streaming-drive.com | 0.8% | 3365 | 77.73.67.23 | https://archive.ph/KW2Lii |
| deregular.xyz | 1.0% | 4251 | 77.73.67.23 | https://archive.ph/SZBMu |
| builderbook.info | 2.4% | 9794 | 94.242.50.119 | https://archive.ph/QXs9r |
| dri-ve-buil-der.buzz | 5.3% | 21831 | 77.73.67.23 | https://archive.ph/NuZzU |
Additional Sources of Referral Traffic (38%)
The following classifications of referral sources do not fit into the category of obvious subscription traps: Merchant Services, Account Trading, Software or Services, Casinos, Banking Institutions, Media Coverage, Games, and Internal Links. Snopes was unable to classify URLs linked to just over 3% of Maxpay's traffic.
Merchant services refer to a variety of URLs that appear to be associated with external financial services. Snopes classifies 15% of Maxpay referral traffic in this category. The most prominent example is arcot.com, which is a "payment authentication network." Another example is netteller.com, which is "a digital wallet that makes managing your money quick, easy and secure."
Account trading refers to websites that sell "premium access" to a variety of domain names associated with file sharing. 14% of traffic to Maxpay falls into this category. Premium access offers faster upload and download speeds on file sharing sites. Two companies appear in the referral data — hkaccounttrading.com and centercoast.net.
In the case of these two companies — which offer premium access to the same collection of domains — successful transactions require the seller to have a pre-existing relationship with the buyer via a third party website:
Software or services (3.2%) include what appear to be actual products. The most prominent example is an iPhone surveillance service named mSpy (1.1% of referral traffic). The company markets itself as a way to monitor children's safety. ClickDealer advertises the project as a way to spy on unfaithful romantic partners.
Communication between maxpay.com and online gambling operations account for another 0.6% of referral traffic. Two casino brands appear in the referral traffic: 22bet and mr.bet. Games (0.2%), a separate category, involves what are potentially functional non-gambling games that require payment to play.
Referrals that stem from actual links contained in media reports (0.6%) fall into the category of media coverage. Internal links refer to communication between Maxpay and internal or customer service communication products like zendesk.
Finally, 0.4% of referral traffic stems from an actual bank based in Latvia. We classify this as a "banking institution." That bank is Latpastabanka AS, also known as LPB Bank.