In August 2017, news appeared that hundreds of millions of e-mail addresses were harvested by a "spambot" with the goal of using them to spread information-stealing malware internationally.
According to security expert Troy Hunt, the "onliner spambot" has found 711 million emails, in part by gathering emails exposed in data breaches. Hunt wrote that the amount of data was so large that it accounted for "almost one address for every single man, woman and child in all of Europe." He also said that his own e-mail address had been compromised:
I have no idea how this service got mine, but even for me with all the data I see doing what I do, there was still a moment where I went "ah, this helps explain all the spam I get". And that's the unfortunate reality for all of us: our email addresses are a simple commodity that's shared and traded with reckless abandon, used by unscrupulous parties to bombard us with everything from Viagra offers to promises of Nigerian prince wealth. That, unfortunately, is life on the web today.
Hunt said that he was alerted to the issue by a security researcher who identifies himself as Benkow. Since then, he said, they have tracked the source of the spambot to the Netherlands and "have been in touch with a trusted source there who's communicating with law enforcement in an attempt to get it shut down ASAP". Benkow wrote on his blog on 29 August 2017:
This spambot is used since at least 2016 to spread a banking trojan called Ursnif. I have seen this spambot targeting specific countries like Italy, or specific business like Hotels.
He also said said that the spambot has caused "more than 100,000 unique infections". The Ursnif malware, once it infects a computer, can monitor your web activity, steal information, and even take screenshots of your computer.
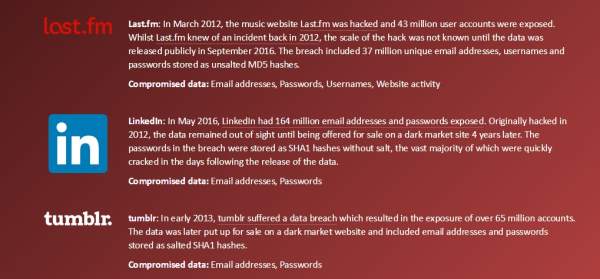
Hunt, a regional director for Microsoft, wrote that while the spambot collected 711 million email addresses, many of them were pulled from the web with extra characters or "junk" attached to them, making them unusable by the spambot. He told us that he believed that the email addresses affected had been "previously exposed." Some of the passwords the spambot grabbed came from email accounts, while others were connected to websites that had been hit in prior attacks.
To help email holders determine whether their addresses were compromised, Hunt recorded the millions of emails the spambot seized (without the related passwords) on his own website, Have I Been Pwned? or HIBP for short.
The site, created in 2013 in the wake of an Adobe data breach, allows visitors to see if their email accounts have been compromised by entering their email — but, again, not their password or private information. The site then tells users if the account was exposed in a cyber attack and, if it was, which sites were compromised and what information was compromised in the attack:
HIBP also shows users whether their accounts have been "pasted," exposing them to further risk:
A "paste" is information that has been "pasted" to a publicly facing website designed to share content such as Pastebin. These services are favoured by hackers due to the ease of anonymously sharing information and they're frequently the first place a breach appears.
HIBP searches through pastes that are broadcast by the @dumpmon Twitter account and reported as having emails that are a potential indicator of a breach. Finding an email address in a paste does not immediately mean it has been disclosed as the result of a breach. Review the paste and determine if your account has been compromised then take appropriate action such as changing passwords.
Concern over the massive amount of data seized by the "onliner" fueled a surge in interest in Hunt's site; he told us that at one point, HIBP was visited by more than 17,000 active users. He also said that the "onliner" is still active in the Netherlands, and that he is continuing to work with a contact who is communicating with Dutch law enforcement to get it taken down.