On 14 June 2016, multiple news outlets reported that the Democratic National Committee (DNC) and security firm Crowdstrike had confirmed a DNC computer network security breach for which they maintained unspecified Russian operatives were responsible:
Russian hackers penetrated the Democratic National Committee's computer network, compromising a a raft of information including research on presumptive Republican nominee Donald Trump, officials confirmed.
“The security of our system is critical to our operation and to the confidence of the campaigns and state parties we work with,” said Rep. Debbie Wasserman Schultz of Florida, the DNC chairwoman. “When we discovered the intrusion, we treated this like the serious incident it is and reached out to CrowdStrike immediately. Our team moved as quickly as possible to kick out the intruders and secure our network.”
CrowdStrike, a cyber security firm, also confirmed the hack Tuesday, saying that its origins pointed to the Russian government.
The DNC and CrowdStrike both suggested that the security breach had occurred over the course of "months," and that "a raft of information including research on presumptive Republican nominee Donald Trump" had been compromised. The story remained one of largely technology-centric interest until additional information of indeterminate provenance appeared the following day.
The day after the DNC and CrowdStrike admitted the breach and pegged Russian spies as the culprits, a purported hacker calling himself Guccifer 2.0 (not to be confused with a separate hacker known as Guccifer) set up a single-post WordPress blog. In that 2016 blog, Guccifer 2.0 tauntingly claimed responsibility for the DNC network breach:
Worldwide known cyber security company CrowdStrike announced that the Democratic National Committee (DNC) servers had been hacked by “sophisticated” hacker groups.
I’m very pleased the company appreciated my skills so highly))) But in fact, it was easy, very easy.
Guccifer may have been the first one who penetrated Hillary Clinton’s and other Democrats’ mail servers. But he certainly wasn’t the last. No wonder any other hacker could easily get access to the DNC’s servers.
Shame on CrowdStrike: Do you think I’ve been in the DNC’s networks for almost a year and saved only 2 documents? Do you really believe it?
Here are just a few docs from many thousands I extracted when hacking into DNC’s network.
By way of proof, Guccifer 2.0 published a smattering of purported DNC documents obtained in the breach while promising that a far larger cache had been turned over to the notorious WikiLeaks web site. That claim coincided with statements made by WikiLeaks founder Julian Assange a few days earlier in an interview about Hillary Clinton-related e-mail leaks:
Julian Assange, the founder of WikiLeaks, has said his organisation is preparing to publish more emails Hillary Clinton sent and received while US secretary of state.
Clinton, the presumptive Democratic presidential nominee, is under FBI investigation to determine whether she broke federal law by using her private email in sending classified information. A new WikiLeaks release of Clinton emails is likely to fan a controversy that has bedevilled her campaign and provide further ammunition for Donald Trump, her Republican presidential rival, who has used the issue to attack her.
Assange’s comments came in an interview on ITV’s Peston. “We have upcoming leaks in relation to Hillary Clinton ... We have emails pending publication, that is correct,” Assange said. He did not specify when or how many emails would be published.
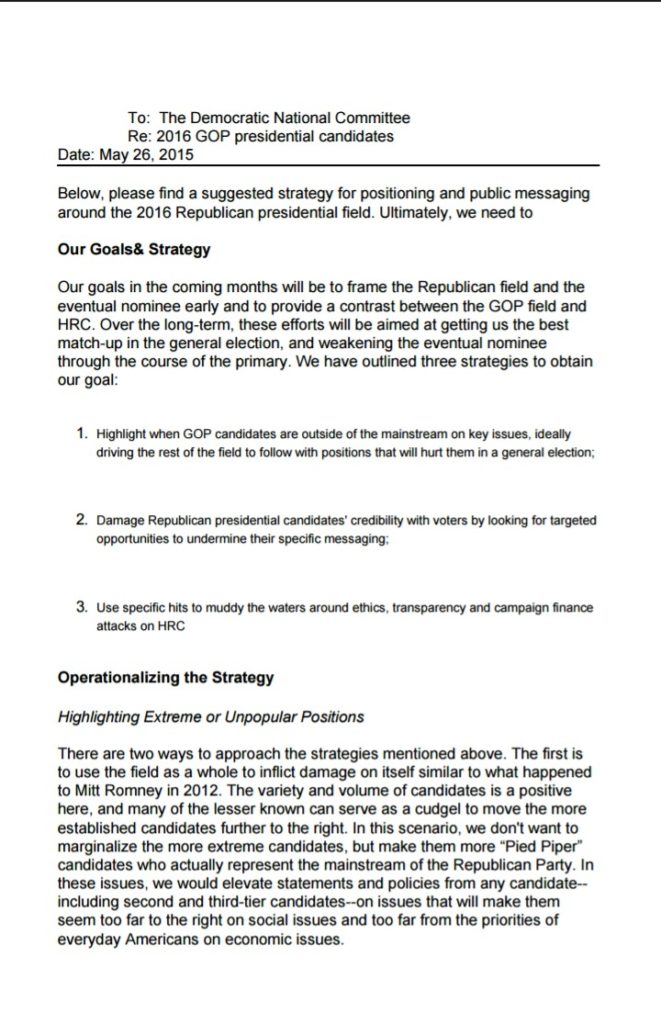
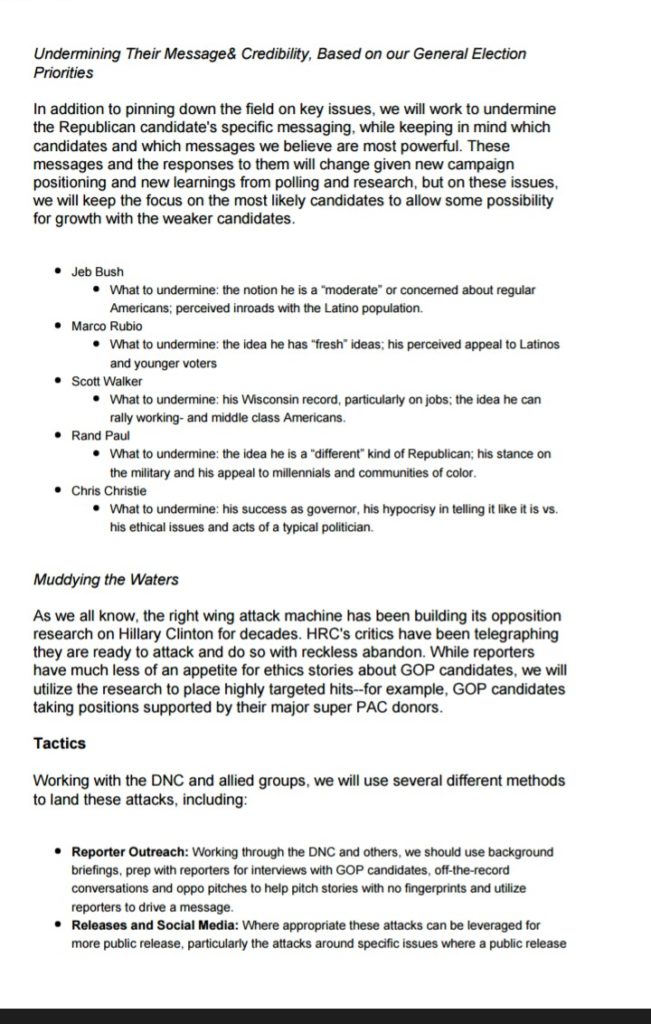
Among the donor lists and other documents purportedly grabbed by Gucci 2.0 was material that struck a chord among supporters of Democratic presidential candidate Bernie Sanders by suggesting that the DNC had strategized to collude with the news media in promoting Sanders' rival, Hillary Clinton, long before the nomination process was completed:
New York Daily News columnist Shaun King, a Sanders supporter, called the documents "disturbing" if authentic, citing portions of the strategy that outlined utilizing news outlets "to drive a message ...with no fingerprints":
The DNC is supposed to be an unbiased arbiter of the campaign and this memo suggests anything but that. Furthermore, the memo gives strategies for they can best position her for general election. One of those strategies says they aim to, "Use specific hits to muddy the water around ethics, transparency, and campaign finance attacks on HRC."
How ugly is that? Muddying the water? What a mess.
Another memo claims that they "will utilize reporters to drive a message" but do so "with no fingerprints" on the process so that the public believes the messages are coming from the reporters and not the campaign.
This is exactly what many of us have suspected was going on for the past year.
Well before Julian Assange's comments, the DNC's confirmation, or Guccifer 2.0's claims, Daily Beast journalist Olivia Nuzzi had referenced one such "no fingerprints" pitch she said she had received:
Maybe I would buy into "bernie bros" more if I hadn't been pitched a story about bernie bros by Hillary's camp.
— Olivia Nuzzi (@Olivianuzzi) June 8, 2016
Gawker also reported that additional related information had been released exclusively to them and that they had authenticated some of it:
According to the metadata associated with the file, the Trump dossier was last saved by someone named (in Cyrillic letters) “Felix Edmundovich.” This could be a reference to the historical Soviet figure known as “Iron Felix,” and is likely an alias. The hackers were able to access opposition files and may have been able to read email and chat traffic, but did not touch any financial, donor, or personal information, the DNC said. However, the user who sent the files to Gawker refuted that claim, writing, “DNC chairwoman Debbie Wasserman Schultz said no financial documents were compromised. Nonsense! Just look through the Democratic Party lists of donors! They say there were no secret docs! Lies again! Also I have some secret documents from Hillary’s PC she worked with as the Secretary of State.” Among the files sent to Gawker are what appear to be several lists of donors, including email addresses and donation amounts, grouped by wealth and specific fundraising events. Gawker has not yet been able to verify that the Trump file was produced by the DNC, but we have been able to independently verify that the financial documents were produced by people or groups affiliated with the Democratic Party.
The Trump campaign responded to the news with an entirely separate theory, speculating that the DNC themselves had staged the "hack":
NEW - Trump statement on Gawker report of alleged DNC oppo file - "we believe DNC did the 'hacking" pic.twitter.com/Euwlko9Fex
— John Santucci (@JTSantucci) June 15, 2016
Ars Technica culled information suggesting that if the breach didn't originate in Russia, then whoever was responsible tinkered with metadata to create that impression:
Exhibit A in the case is this document created and later edited in the ubiquitous Microsoft Word format. Metadata left inside the file shows it was last edited by someone using the computer name "Феликс Эдмундович." That means the computer was configured to use the Russian language and that it was connected to a Russian-language keyboard. More intriguing still, "Феликс Эдмундович" is the colloquial name that translates to Felix Dzerzhinsky, the 20th Century Russian statesman who is best known for founding the Soviet secret police. (The metadata also shows that the purported DNC strategy memo was originally created by someone named Warren Flood, which happens to be the name of a LinkedIn user claiming to provide strategy and data analytics services to Democratic candidates.) Exhibit B is this opposition research document on Donald Trump, the presumptive Republican presidential nominee. Exhibit B is also written in Word. Several of the Web links in it are broken and contain the error message "Error! Hyperlink reference not valid." But in a PDF-formatted copy of the same document published by Gawker a few hours before Guccifer 2.0's post went live, the error messages with roughly the same meaning appear in Russian ... The other piece of evidence is more circumstantial, but it still strengthens the case that the person publishing the documents intentionally or unintentionally left Russian—or at least Eastern European—fingerprints on the leak. It's the use of ")))" in the accompanying blog post. That's a common way people in Eastern Europe and Russia denote a smiley in text.
All three pieces of evidence were teased out of the documents and noted on Twitter by an independent security researcher who goes by the handle PwnAllTheThings. The theory is also consistent with everything previously published by CrowdStrike, the security firm the DNC hired to investigate its suspicions that its servers had been breached. CrowdStrike researchers said they quickly determined that the servers had been infiltrated by two separate Russian hacking groups. In response to Wednesday's leak, CrowdStrike raised the possibility that the leak was part of a Russian Intelligence disinformation campaign. Company officials declined to comment on Thursday for this post. "There's also the fact that the hacker is publishing documents at all, which rules out lots of nation-states," the PwnAllTheThings researcher told Ars in a private message. "China, for example, would happily spy on the DNC to try and get the Trump oppo [opposition] research to support their foreign policy objectives, but they wouldn't publish the documents to influence the election." Dave Aitel, CEO of Immunity Security, a firm that provides advanced hacking tools to security professionals, agreed with the researcher's theory. "I think his analysis is very believable when you look at what CrowdStrike is saying and when you look at what other people are not saying," Aitel told Ars. "You don't have the FBI or DHS coming out and saying: 'Hey we don't think it's Russia.' If it is Russia, a nation state, it's a pretty big deal. Otherwise the FBI would say: 'We're conducting an investigation.' But they're not saying that." Of course, it's still possible that the Russian fingerprints were left intentionally by someone who has no connection to Russia, or by a Russian-speaking person with no connection to the Russian government, or any number of other scenarios. The abundance of plausible competing theories underscores just how hard it is to accurately attribute attacks online and how perilous it is to reach summary conclusions.
Jordan Chariton of The Young Turks pursued the DNC for a denial of the documents' authenticity, receiving first what he described as a "vague" response and no other comment:
When I pushed back 2 DNC on its vague, non-answer 2 my question, they wouldn't provide on-the-record response pic.twitter.com/IaU9KzHjcC — Jordan (@JordanChariton) June 16, 2016
Still no on record denial from DNC- 2 be clear, there's NO CONFIRMATION this is authentic, but DNC silence deafening pic.twitter.com/Djcw5gFgw0
— Jordan (@JordanChariton) June 16, 2016
24 hours later, still no on-the-record denial from DNC as to authenticity of email showing clear collusion b/w it and @HillaryClinton — Jordan (@JordanChariton) June 17, 2016
By 17 June 2016, the only update to the initial confirmation of the hack provided by the DNC and CrowdStrike were unverified claims released by a hacker going by the name of Guccifer 2.0. The DNC has so far declined to comment on the authenticity of the documents leaked on 15 June 2016, and no one has definitively identified any parties responsible for the hack. And WikiLeaks hasn't published any additional information since Julian Assange's 12 June 2016 statement about an impending document dump of Hillary Clinton e-mails.