Generally speaking, malicious actors have tried to spread malware via various online maps by disguising it as information from credible sources about the global spread of COVID-19.
However, the real-time map from Johns Hopkins University showing the spread of COVID-19 is itself safe and does not contain malware.
In March 2020, as the outbreak of the novel coronavirus grew into a global pandemic, worried citizens of the world took to the internet in search of information about the disease caused by the virus, COVID-19. They turned to organizations such as the Centers for Disease Control and Prevention (CDC) and the World Health Organization (WHO) to get an accurate picture of how fast the disease was spreading, where cases were being reported, and what they should do to keep themselves (and their communities) safe.
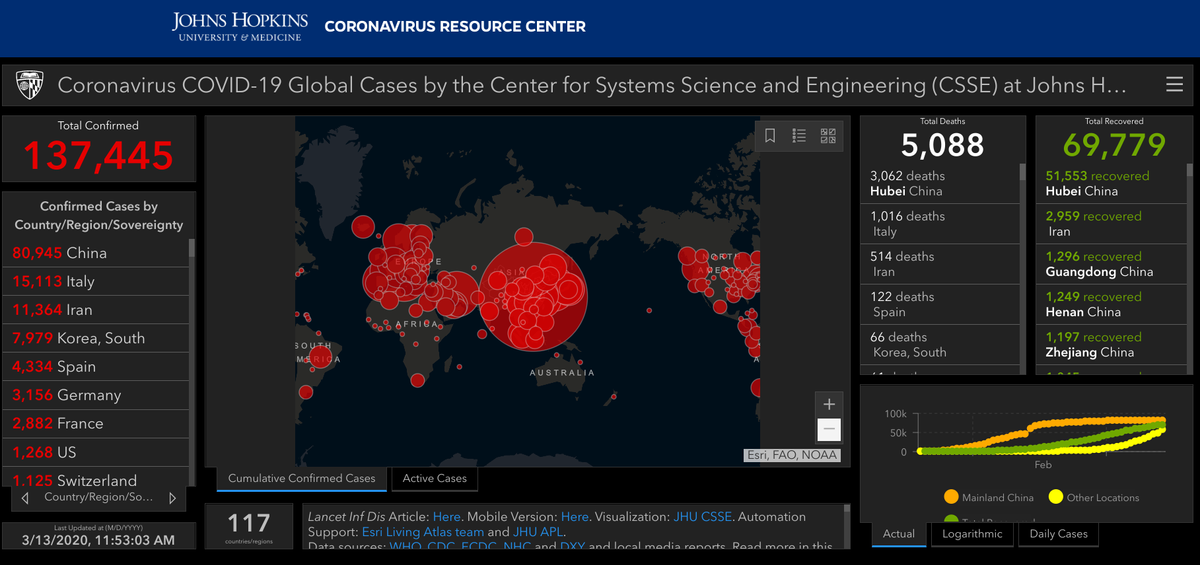
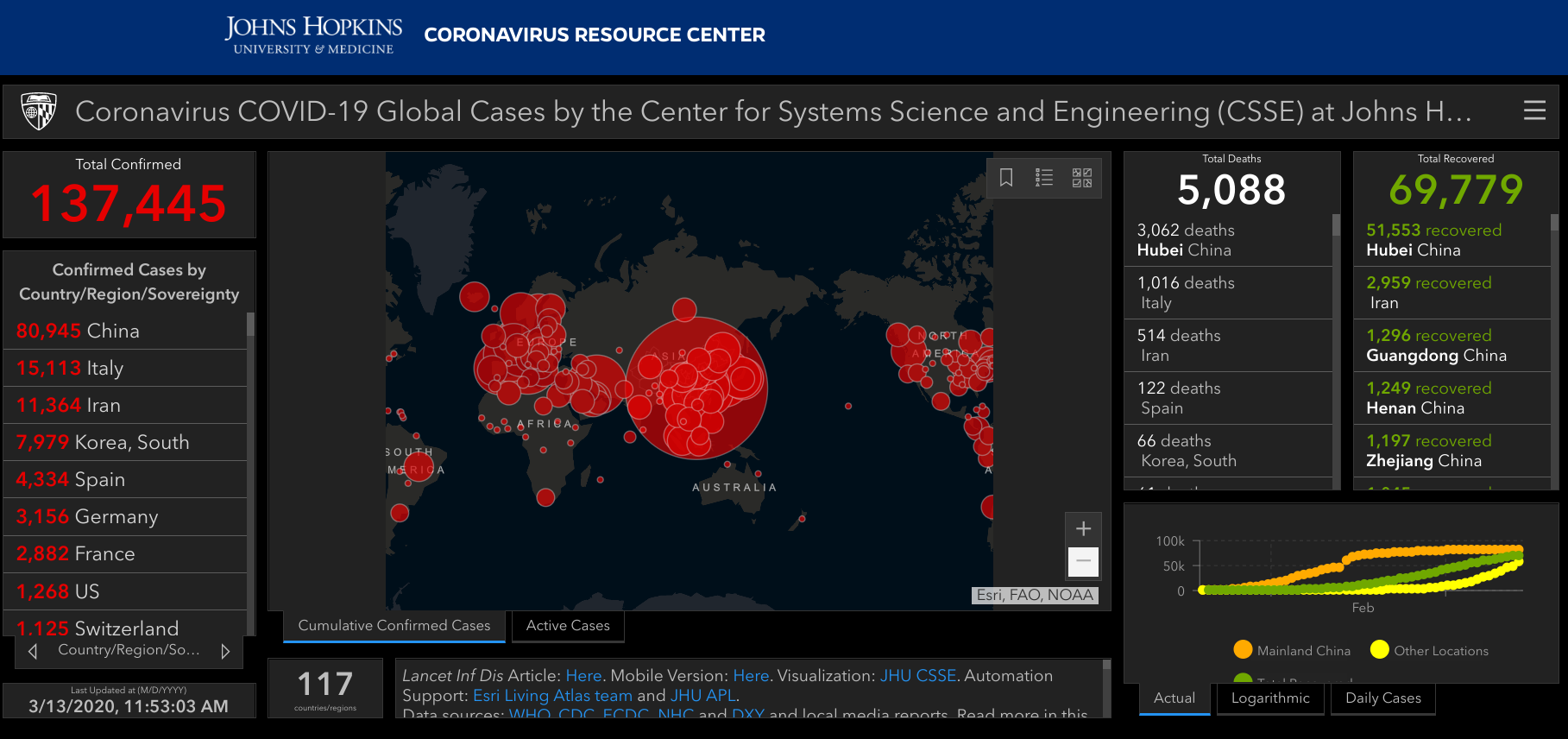
Johns Hopkins University also provided a valuable resource in the form of a real-time map that showed how the disease was spreading around the globe. At the time of this writing, the map from Hopkins' Coronavirus Research Center shows 137,445 total confirmed cases that have resulted in just over 5,000 deaths.
This is a genuine map from Johns Hopkins that is safe to access here.
Unfortunately, malicious actors saw the heightened concerns about COVID-19 as an opportunity to start spreading misinformation and malware. On March 9, 2020, Reason Security released a report stating that maps similar to the one above were being used to trick people into downloading malware:
As global awareness of a Coronavirus pandemic gradually gives way to full out panic, and as governments begin ramping up their efforts to combat the virus and protect its citizens, global news agencies find themselves racing to answer the public’s demand for accurate information about new Corona related infections, deaths, transmissions, etc.
This demand creates a vulnerability that malicious actors have quickly taken advantage of by spreading malware disguised as a “Coronavirus map”. Reason Labs’ cybersecurity researcher, Shai Alfasi, found and analyzed this malware that had weaponized coronavirus map applications in order to steal credentials such as user names, passwords, credit card numbers and other sensitive information that is stored in the users’ browser. Attackers can use this information for many other operations as well, such as selling it on the deep web or for gaining access to bank accounts or social media.
Hacker News explained that this malware attack targets people who are searching for any maps about COVID-19 and tricks them into downloading a map with a file that runs a malicious application on the user's computer. Once downloaded, the map appears similar to the legitimate map from Johns Hopkins shown above, but the software will actually compromise the computer and attempt to steal personal information, such as passwords and credit card information.
The malware attack specifically aims to target those who are looking for cartographic presentations of the spread of COVID-19 on the Internet, and tricks them to download and run a malicious application that, on its front-end, shows a map loaded from a legit online source but in the background compromises the computer.
The real map from Johns Hopkins is viewable online and does not require you to download any software to use it. You can access the real-time tracking map by visiting this website. This is the official URL from Johns Hopkins, and no indication exists that this site is unsafe or infected with malware.
ESRI, the company that provided the geographic information system (GIS) software to create Johns Hopkins' real-time coronavirus tracking map, attempted to clear up some of the confusion in a blog post. The company explained that the real online map found on Johns Hopkins' site "does NOT contain any malware (and NEVER contained malware)." The reports from Hacker News and the like are referring to a scam that uses an impostor version of the Hopkins map to trick users into downloading malware.
ESRI writes (emphasis ours):
An increasing number of articles have been published on the Internet with unclear and sometimes misleading information concerning one of the primary dashboards for awareness concerning the spread of the Coronavirus. To be clear, the online map posted by Johns Hopkins University at https://coronavirus.jhu.edu/map.html does NOT contain any malware (and NEVER contained malware). This popular dashboard web application is hosted by Esri as part of our ArcGIS Online offering.
The confusion comes from an issue where a malicious person created a downloadable Windows-based application containing malware whose display is practically identical to the Johns Hopkins Coronavirus browser-based dashboard (see comparison figure below). Whomever posted the malicious downloadable app is attempting to take advantage of the hype around the Coronavirus, but it requires the user to either download the app executable, or it could be distributed by email for the user to then install onto their local Windows system.
The malicious app once downloaded and installed deploys malware called AZORult which is designed to steal credentials in the background (among other activities). To make the user think they are getting a Coronavirus map viewer, the app calls the URL of the Johns Hopkins dashboard and displays the results inside the application window.
Bottom-line, you are fine browsing the Coronavirus dashboard on the web with your browser as no software needs to be downloaded. If you come across someone offering a Coronavirus dashboard where you need to download software to view it, don’t use it!
In summary, a real-time map that tracks the spread of COVID-19 around the globe is available to view on the Johns Hopkins University website. This map is safe to use and does not require you to download any software. If you encounter an email or social media post that asks you to download a similar map, be cautious. It's likely someone is attempting to trick you into downloading a piece of malware.